The Critical Role of Cybersecurity in SCADA Systems Protection
Supervisory Control and Data Acquisition (SCADA) systems are vital for the seamless operation of industries such as energy, transportation, manufacturing, and water treatment. These systems ensure that industrial processes run efficiently, making them indispensable in modern infrastructure. However, with the increasing integration of technology, cybersecurity in SCADA systems is becoming a prime target for cyberattacks. As industries become more connected, the need for robust cybersecurity measures to protect SCADA systems has never been greater.
Understanding SCADA Systems and Their Importance
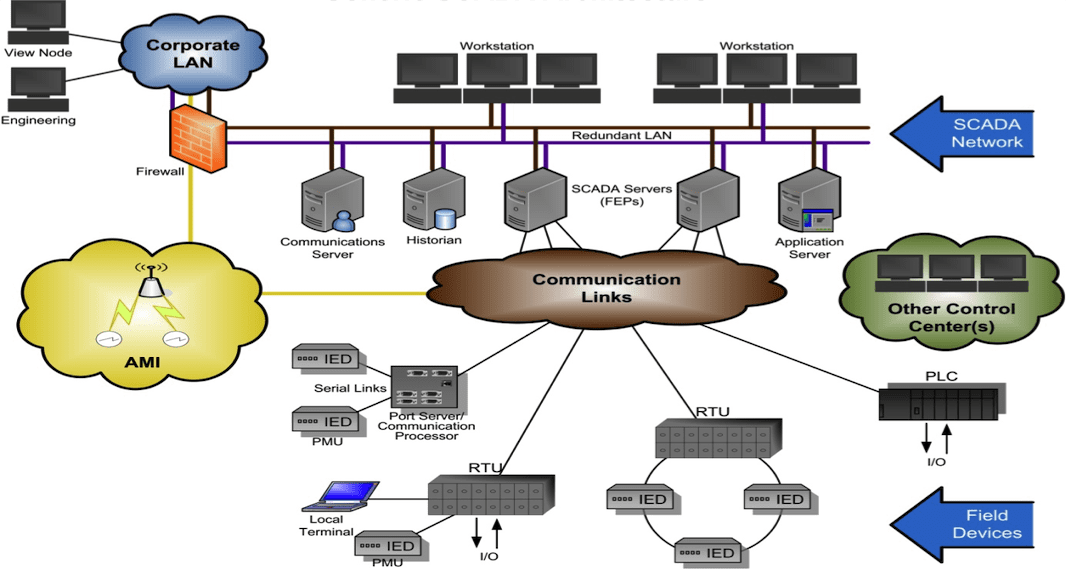
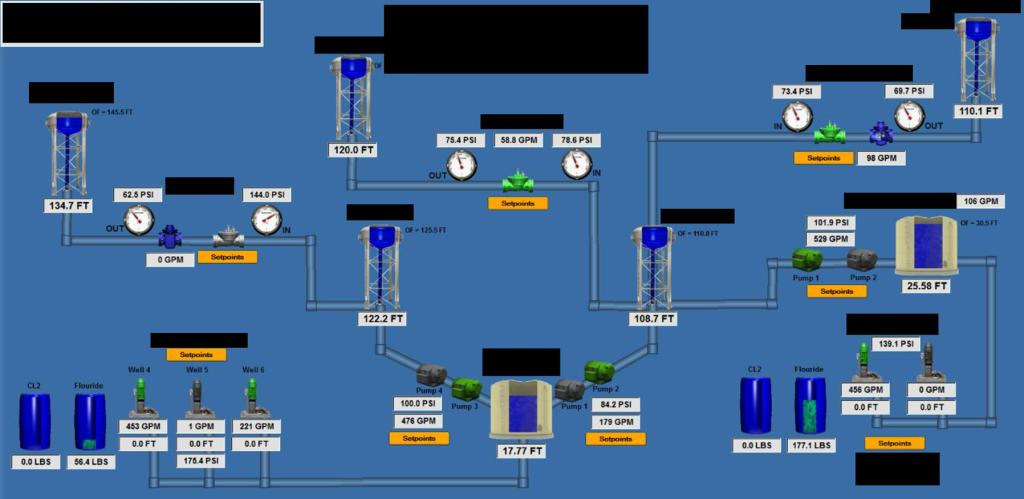
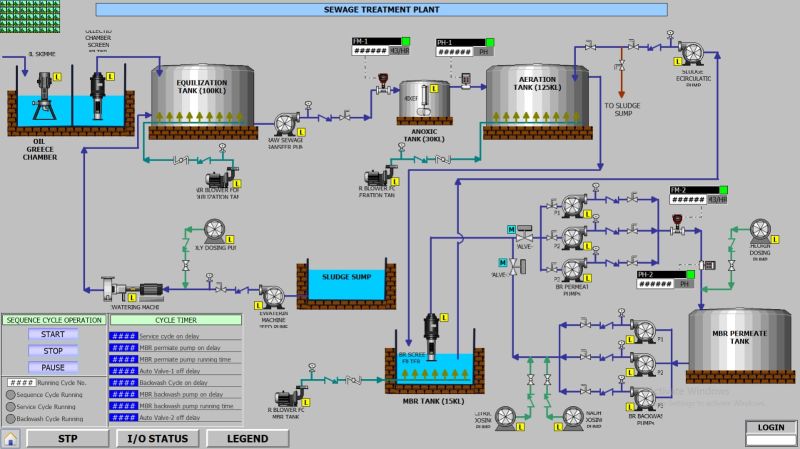
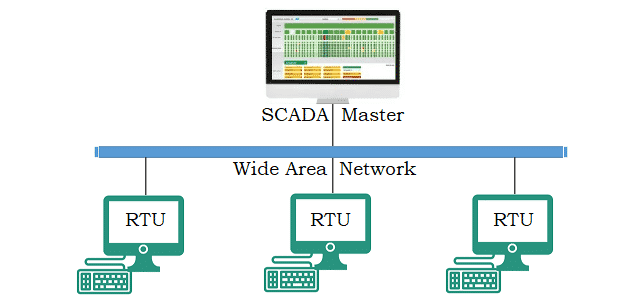
Cybersecurity in SCADA systems are a combination of hardware and software used for industrial automation and control. They collect data from sensors, process it, and enable operators to monitor and control processes in real time. From regulating power grids to managing water supply systems, SCADA systems form the backbone of critical infrastructure.
Key Functions of SCADA Systems:
- Data Acquisition: Collecting real-time data from sensors and field devices.
- Supervisory Control: Allowing operators to make informed decisions and adjustments.
- Alarm Management: Notifying operators of anomalies or potential failures.
- System Monitoring: Offering insights into system performance and health.
Given their critical role, any disruption to SCADA systems can have catastrophic consequences, ranging from operational downtime to public safety risks.

The Growing Cybersecurity Threat to SCADA Systems
The increasing connectivity of SCADA systems to the internet has introduced vulnerabilities that can be exploited by malicious actors. Historically, SCADA systems were isolated from external networks, known as “air-gapped” systems, making them relatively secure. However, the rise of Industrial Internet of Things (IIoT) devices and remote monitoring has bridged this gap, exposing SCADA systems to cyber risks.
Common Cybersecurity Threats to SCADA Systems:
Malware can disrupt operations, corrupt data, or lock systems until a ransom is paid.
Overloading the system with traffic to render it inoperable.
Unauthorized actions by employees or contractors.
Attacks targeting previously unknown vulnerabilities.
Intercepting and altering communications between devices.
These threats highlight the urgency for industries to prioritize cybersecurity measures to safeguard their SCADA systems.
Why Cybersecurity is Critical for SCADA Systems
The impact of a cyberattack on SCADA systems extends far beyond the targeted organization. It can disrupt essential services, compromise public safety, and damage national security. Here are some reasons why cybersecurity is indispensable for SCADA systems:
1. Protection of Critical Infrastructure
SCADA systems manage critical infrastructure like power plants, water treatment facilities, and transportation networks. Cyberattacks on these systems can lead to widespread outages, contamination of water supplies, or transportation delays, causing significant societal and economic disruption.
2. Ensuring Data Integrity
SCADA systems rely on accurate data to make real-time decisions. A cyberattack that compromises data integrity can lead to faulty operations, endangering lives and property.
3. Preventing Financial Loss
Operational downtime caused by cyberattacks can result in hefty financial losses. Companies may face penalties for failing to deliver services, repair costs, and reputational damage.
4. Compliance with Regulations
Governments worldwide have established regulations to ensure the cybersecurity of critical infrastructure. Non-compliance can result in legal penalties and loss of business licenses.
Key Strategies to Enhance Cybersecurity in SCADA Systems
Securing SCADA systems requires a multi-layered approach that combines technology, policies, and continuous monitoring. Below are essential strategies to fortify SCADA cybersecurity:
1. Network Segmentation
Isolating SCADA networks from other IT networks minimizes the risk of lateral movement by attackers. By implementing firewalls and Virtual Local Area Networks (VLANs), organizations can limit access to SCADA systems.
2. Implementing Strong Access Controls
Using multi-factor authentication (MFA) and role-based access controls ensures that only authorized personnel can access SCADA systems. Regularly updating passwords and revoking access for former employees further strengthens security.
3. Regular Vulnerability Assessments
Conducting periodic vulnerability assessments helps identify and address weaknesses in the system. These assessments should be complemented by penetration testing to simulate real-world attack scenarios.
4. Real-Time Monitoring and Incident Response
Deploying intrusion detection and prevention systems (IDPS) enables real-time monitoring of network traffic for suspicious activity. Additionally, establishing a robust incident response plan ensures a swift and coordinated reaction to cyberattacks.
5. Patching and Updating Software
Outdated software is a common entry point for attackers. Regularly applying patches and updates to SCADA software and associated systems can prevent exploitation of known vulnerabilities.
6. Training and Awareness Programs
Employees play a critical role in cybersecurity. Conducting regular training sessions and awareness programs equips staff with the knowledge to identify and report potential threats.
Real-World Implications of Inadequate Cybersecurity in SCADA
The consequences of neglecting SCADA cybersecurity have been demonstrated in several high-profile incidents:
- Stuxnet (2010): This sophisticated worm targeted Iran’s nuclear facilities, highlighting the vulnerabilities of SCADA systems to cyber warfare.
- Colonial Pipeline Attack (2021): A ransomware attack on the Colonial Pipeline disrupted fuel supply across the Eastern United States, underscoring the need for robust cybersecurity in critical infrastructure.
- Water Treatment Facility Hack (2021): In Florida, hackers attempted to alter the chemical levels in a water treatment plant, posing a serious threat to public health.
These incidents emphasize that the stakes are too high to ignore SCADA cybersecurity.
Emerging Technologies for Cybersecurity in SCADA
Advancements in technology are offering new tools to bolster SCADA cybersecurity. These innovations are critical in staying ahead of evolving cyber threats.
1. Artificial Intelligence (AI) and Machine Learning
AI-powered tools can analyze vast amounts of data to detect anomalies and predict potential threats. Machine learning algorithms can continuously improve detection capabilities, making it harder for attackers to evade defenses.
2. Blockchain Technology
Blockchain’s decentralized and immutable nature makes it an excellent tool for ensuring data integrity in SCADA systems. It can be used to securely log transactions and prevent unauthorized modifications.
3. Zero Trust Architecture
The Zero Trust model assumes that no user or device is trusted by default, even if they are within the network perimeter. This approach involves verifying every access request and minimizing privileges, significantly reducing the risk of unauthorized access.
A Call to Action
As SCADA systems become increasingly interconnected, their vulnerability to cyber threats grows. Cybersecurity is no longer optional but a fundamental requirement for the safe and efficient operation of critical infrastructure. Organizations must adopt a proactive approach by implementing robust security measures, leveraging emerging technologies, and fostering a culture of cybersecurity awareness.
Protecting SCADA systems is not just about safeguarding industrial processes; it is about ensuring public safety, economic stability, and national security. By prioritizing cybersecurity, industries can fortify their SCADA systems against evolving threats, paving the way for a resilient and secure future.




