Protect Your Systems: SCADA Attacks – Lessons from 3 Real-World Disasters
Anatomy of a SCADA Attacks: 3 Real-World Breaches and the Lessons Learned
For years, major scada attacks felt theoretical to many plant managers—a distant threat seen in movies. Today, that is dangerously no longer the case. As industrial facilities embrace the efficiency of the Industrial Internet of Things (IIoT) and remote connectivity, the attack surface for critical infrastructure has expanded dramatically. Understanding the real-world scada vulnerabilities that have led to disaster is the first step in building a resilient defense for your own operations.
This article dissects three of the most significant scada attacks in recent history. We will analyze how each breach occurred, the critical lessons learned, and the practical steps you can take to ensure your facility doesn’t become the next headline.
Table of Contents
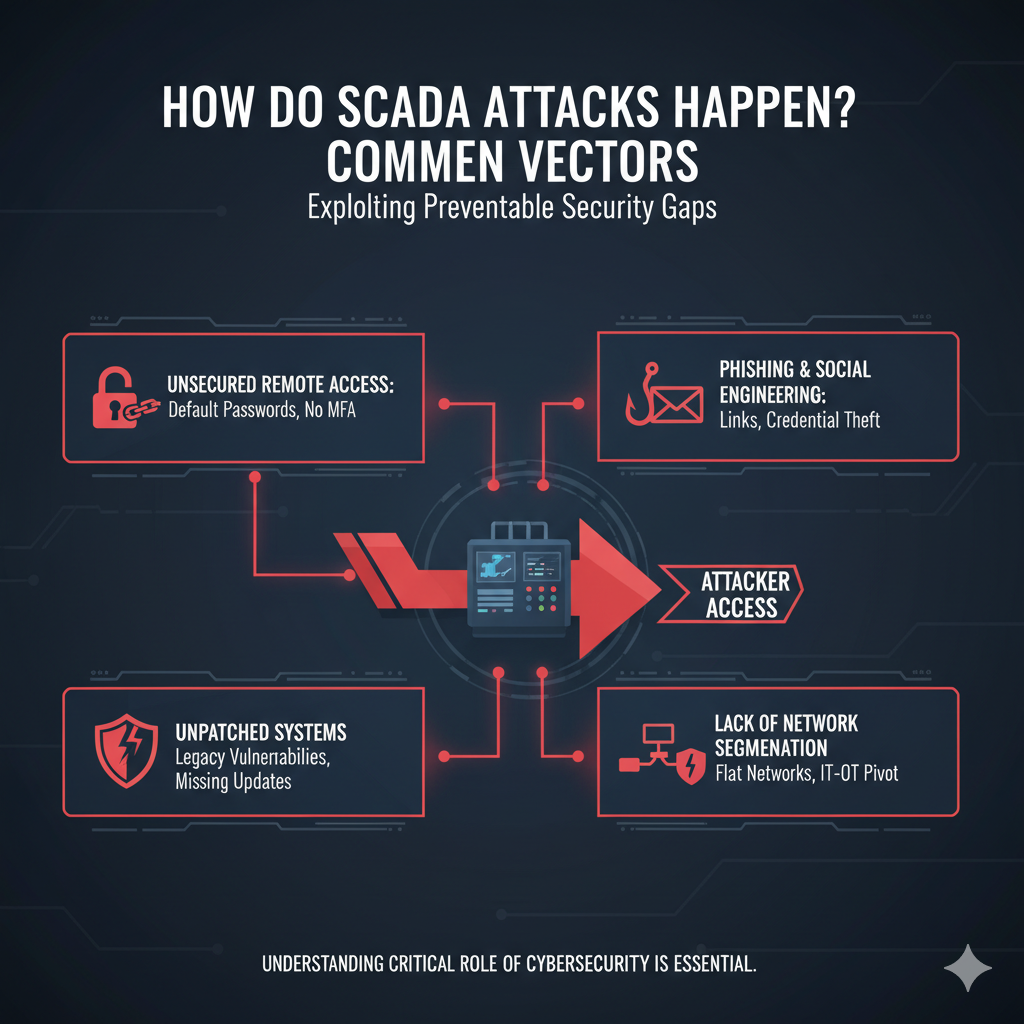
How Do SCADA Attacks Happen? Common Vectors
While some attacks are highly sophisticated, most successful breaches exploit common, preventable security gaps. Understanding the critical role of cybersecurity is essential. Attackers typically gain access to Industrial Control Systems (ICS) through:
- Unsecured Remote Access: Using default passwords or failing to implement Multi-Factor Authentication (MFA) on remote access software is a primary entry point.
- Phishing and Social Engineering: Tricking an employee into clicking a malicious link or revealing their credentials remains a highly effective tactic.
- Unpatched Systems: Legacy SCADA systems that are missing critical security patches contain known scada vulnerabilities that are easily exploited.
- Lack of Network Segmentation: A “flat” network where the corporate IT systems and the operational technology (OT) systems can freely communicate allows an attacker who breaches the office to pivot directly to critical plant controls.
Case Study 1: The Oldsmar, Florida Water Treatment Plant (2021)
The Story: In February 2021, an operator at the Oldsmar water treatment facility watched in real-time as their cursor was remotely moved across the HMI screen. The attacker attempted to increase the level of sodium hydroxide (lye) in the water supply by over 100-fold, a change that could have poisoned thousands of citizens. The operator was able to immediately reverse the command, averting disaster, as reported by outlets like WIRED.
The Vulnerability
The plant was using TeamViewer for remote access, and it was configured with a shared password and insufficient firewall protection, making it directly accessible from the internet. This is a common issue for many rural water treatment facilities.
The Lesson
Securing remote access is non-negotiable. This incident is a stark reminder that convenience cannot come at the cost of security. Any system that allows for remote control of physical processes must be protected by multiple layers of security. For a deeper dive into this specific area, see our complete guide to water treatment SCADA security.

Case Study 2: The Colonial Pipeline Ransomware Attack (2021)
The Story: In May 2021, the largest fuel pipeline in the United States, Colonial Pipeline, was forced to shut down its entire operation for several days, leading to widespread fuel shortages. This was not a direct attack on their SCADA system, but a ransomware attack on their IT business network.
The Vulnerability
The attackers gained entry to the IT network through a single compromised password for a VPN account that did not have MFA enabled. According to a Cybersecurity and Infrastructure Security Agency (CISA) advisory, the company was unsure if the attack had spread to its OT network, forcing the precautionary shutdown due to a critical lack of network segmentation.
The Lesson
Your IT and OT networks must be strictly separated. An attack on your billing system should never have the potential to impact your physical operations. This case demonstrates the absolute necessity of network segmentation. This concept is a core part of creating a modern digital oilfield ecosystem that is both efficient and secure.
Case Study 3: The Ukrainian Power Grid Hack (2015)
The Story: The day before Christmas Eve, hackers successfully launched one of the most well-known scada attacks against three power distribution companies in Ukraine, leaving nearly 250,000 people without electricity for hours. The attackers used the operators’ own systems to remotely open circuit breakers.
The Vulnerability
The initial intrusion was achieved through a classic spear-phishing campaign. Malicious emails with tainted Microsoft Office attachments were sent to IT staff. Once an employee opened the attachment, the BlackEnergy malware was installed, allowing hackers to harvest credentials, pivot to the SCADA network, and eventually seize control.
The Lesson
The human element is often the weakest link. Technology alone cannot stop all scada attacks. This breach underscores the need for comprehensive employee training on identifying phishing attempts, which is one of the top 5 best SCADA security practices, alongside robust endpoint security and a well-rehearsed incident response plan.
How Pro-Tech Builds a Resilient SCADA Security Strategy
Learning from these incidents, it’s clear that a proactive, multi-layered approach to SCADA cyber security is the only way to protect critical operations. At Pro-Tech Systems Group, we don’t treat security as an add-on; it’s a core component of our design and integration philosophy.
- Secure-by-Design Architecture: We address all the lessons learned from past scada attacks. We implement robust network segmentation, design secure remote access solutions with MFA, and ensure every component of your SCADA System is configured for maximum security.
- Vulnerability Assessments: We can audit your existing systems to identify and prioritize the most critical scada vulnerabilities, giving you a clear roadmap for improving your security posture.
- Modernization and Upgrades: We help you migrate from vulnerable legacy equipment to modern, secure control systems that are actively supported and can be properly patched.

Proactive Defense is Your Best Investment
The threat of sophisticated scada attacks is real, but a well-designed and properly maintained system can dramatically reduce your risk. By understanding the tactics of attackers and implementing proven security principles, you can ensure the safety, reliability, and resilience of your operations.
Is your SCADA system prepared for a modern cyber threat? Contact our team today for a comprehensive security and vulnerability assessment.




